Yet with all this activity, there is still a 500-pound gorilla in the room: cloud computing security. Backers proclaim that security is one of the cloud’s strongest features, while detractors say it’s riddled with vulnerabilities.
Which is the truth of these claims about ccloud security? In time-honored fashion of IT issues, it depends.
The definition is simple: cloud security prevents data access and exposure by unauthorized users.
Enterprises have the advantage because they are usually familiar with strong network security, and may already have intrusion detection and robust user authentication behind the firewall and in their private cloud. They naturally look for the same security services in the public cloud. However, cloud security tends to be an upgrade for SMB and midsized businesses. Our comprehensive guide to cloud computing can help you decide which type of cloud service, and which specific company, will work best for your business.
Let’s take a closer look at the risks to cloud security.
When you are moving to cloud storage and cloud computing services, the first thing to do is to understand the level of security on your cloud infrastructure. The minimum security on any cloud should include user authentication, data backup and restore, a network firewall and/or encryption, third party security audits, and breach notification policies.
Stronger security will include features like intrusion detection and remediation, two-factor user authentication, and encryption with keys split between the provider and the customer. Segmentation is also an excellent plan, where data volumes and even workloads can be segmented into lower or higher security policy settings.
On top of a secure cloud, strongly consider Cloud Security Gateways. CSGs operate over multiple security portfolios because they are located on-premise, and are not a proprietary cloud offering. Let’s look at a few of the leading security services provided by cloud companies.
Cloud computing security is a critical topic because most businesses use the cloud in some shape, form, or fashion. There are lots of different ways that they use the cloud: cloud computing with SaaS, IaaS, or PaaS; cloud storage with content repositories and archival; DR spin-up; file sharing and gateways for the far-flung enterprise.
Yet with all this activity, there is still a 500-pound gorilla in the room: cloud computing security. Backers proclaim that security is one of the cloud’s strongest features, while detractors say it’s riddled with vulnerabilities.
Which is the truth of these claims about cloud security? In time-honored fashion of IT issues, it depends.
What is Cloud Security?
The definition is simple: cloud security prevents data access and exposure by unauthorized users.
The definition may be simple but the implementation is not, thanks to the wide range of cloud functions and an increasing amount of cyber-attacks. First, we’re talking about public, private, and hybrid clouds. No single cloud type has a lock on cloud security. And cloud providers run data centers just like the rest of us, and any data center is at some level of risk for intrusion.
Enterprises have the advantage because they are usually familiar with strong network security, and may already have intrusion detection and robust user authentication behind the firewall and in their private cloud. They naturally look for the same security services in the public cloud. However, cloud security tends to be an upgrade for SMB and midsized businesses.
Cloud Security Challenges and Risks
Let’s take a closer look at the risks to cloud security.
Lack of visibility. Visibility in the cloud is very different from a traditional physical environment, like highly virtualized environments in the customer data center. In the cloud, most data traffic is between instances/VMs and only about 20% of that traffic is hitting the network edge. This is where most security tools operate on the theory that hackers will launch intrusion attempts from outside the network. Most of the time they will, but if a hacker has successfully deployed malware on the network then it can operate for months with impunity.
DDoS. Not all attacks are so subtle. Distributed denial of service (DDoS) attacks significantly slow down network traffic, and can bring it to a grinding halt. Some attackers even specialize in presenting their own… creative text and images to users. And DDoS attacks are not particularly difficult to launch.
Shadow IT. These are your own employees. They work outside sanctioned channels to build DIY systems, and may subscribe to cloud computing services without corporate knowledge or blessing. If they have not done their security homework, they represent a real internal danger.
Service provider employees. It happens, much as we hate to admit it. Whether through ignorance or malfeasance, your own provider’s staff may have designs on your data. In the simplest cases, they may commit a crime of opportunity by walking away with a backup. In other cases, an employee may work with outside criminals to steal valuable data.
Bring Your Own Device (BYOB). Most users combine personal and business work on their devices, especially on their personal ones. Most companies allow for this by either ignoring the phenomenon, or attempting to secure employee devices that have access to sensitive data. Since most mobile data is in the cloud, an unencrypted device can be easy pickings to a data thief.
Cloud Security Companies
When you are moving to cloud storage and cloud computing services, the first thing to do is to understand the level of security on your cloud infrastructure. The minimum security on any cloud should include user authentication, data backup and restore, a network firewall and/or encryption, third party security audits, and breach notification policies.
Stronger security will include features like intrusion detection and remediation, two-factor user authentication, and encryption with keys split between the provider and the customer. Segmentation is also an excellent plan, where data volumes and even workloads can be segmented into lower or higher security policy settings.
On top of a secure cloud, strongly consider Cloud Security Gateways. CSGs operate over multiple security portfolios because they are located on-premise, and are not a proprietary cloud offering. Let’s look at a few of the leading ones.
offers extensive security services through an on-premise web gateway. It monitors AWS and Azure as well as cloud applications such as Salesforce. It offers a variety of encryption and decryption policies to choose from.
supports application security and works against shadow IT by detecting unusual or suspicious user activity. It has strong security support for cloud platforms including Salesforce and Office 365.
Cisco CloudLock secures AP-based cloud computing applications and cloud-based application development. It runs across SaaS, IaaS, and PaaS, and orchestrates security settings. It has a particularly strong reporting feature.
concentrates on structured data protection and encrypting devices, which provides much-needed security for BYOB. The vendor also practices advanced key management and encrypts, searches, and filters data in popular cloud applications.
Additional well-known CASBs include Imperva with extensive IaaS security support, Netskope with robust data loss prevention, and Bitglass for traffic detection and ease of use.
Top Benefits of Cloud Security
Protect against DDoS. Cloud security will monitor, identify, and help to remediate DDOS attacks by siphoning heavy traffic to multiple global points. There is nothing transparent about this process; DDoS is a serious cyber-attack and web managers will swing into action. But with DDoS protection, you can defeat an attack without a serious loss of service. The same offering should help you analyze the attack once it’s done.
Keep your applications highly available. Your IT administrators work hard to ensure that on-premise applications and data remain available to users. There’s no difference when you use cloud computing services. Cloud security monitors not only against DDoS attacks, but also a variety of threats and slowdowns caused by attempted intrusions and malware.
Secure your data. Financial motives drive many security breaches. Attackers may insert ransomware for an outright payment or place malware to access and sell valuable information. Even when admirable motives drive an attacker— such as the employee who shared the so-called Panama Papers with journalists— will do major damage to a company’s profitability and reputation.
Compliance. Proving data security is vital to legal and regulatory compliance. When you carry out due diligence with a cloud provider, insist that they include third-party audits and audit reports on your security service level agreement. The cloud provider must be able to prove to the regulatory body as well as the customer that is security meets or surpasses regulatory requirements.
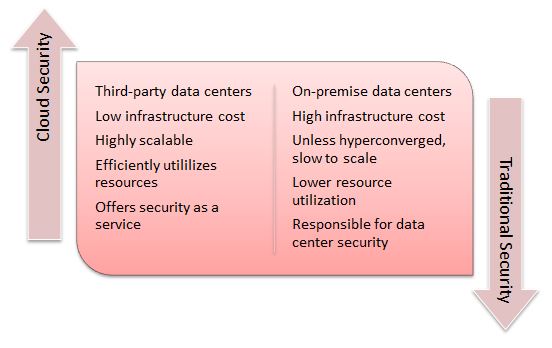
Good economics. Businesses need to invest resources to build their cloud security. However, they already practice traditional security in the data center, and cloud security has some cost advantages that data center security does not.
Finally, the business is ultimately responsible to secure its own applications and data, both on-premise and in the cloud. Too many businesses leave data security to the cloud provider and feel relieved. But they are only putting themselves at more risk, because if a successful attack ferrets out valuable and protected information, the buck stops with the business. Businesses need to understand very well what cloud security measures are in place now, and what cloud security they need to invest in to counter current and future threats.