Cloud computing security is a hot topic these days. Last week, we covered 7 emerging cloud security vendors who are doing their best to make cloud computing every bit as secure – if not more so – than on-premise computing.
Last week’s story featured the likes of Okta, SecureAuth and Symplified. In other words, it was heavy on identity management and access controls – two of the most critical components of secure cloud computing.
This week, we look at virtualization security, security for e-commerce transactions, cloud-based data loss protection and more. Here are 7 more cloud security up-and-comers:
What Problem Do they Solve? With high-profile security breaches, such as those that hit TJX, the VA, the FAA, the DoD, and, well, this list could go on and on, data-loss protection is a critical issue for all organizations. It’s especially an issue for those that must comply with regulations like PCI-DSS, FISMA and HIPPA.
The problem with current Data Loss Protection (DLP) solutions, according to Brad Miller, CEO of Awareness Tech, is that they sit within the corporate network and therefore act in a manner similar to traditional perimeter security. They work well when integrated with Outlook or when blocking USB ports on laptops.
When users are disconnected from the corporate network, when they access their own personal web-based email accounts or when they are using an array of mobile devices, traditional DLP doesn’t keep up.
In other words, Awareness Tech argues that traditional DLP (“traditional” may be a stretch since this is still a fairly new space) is not up to snuff when it comes to cloud computing and mobility.
What they Do: Awareness Tech focuses on insider security risks through its InterGuard suite of products that offer DLP, web filtering, employee monitoring, mobile monitoring and mobile device recovery, remote data retrieval and wiping, and remote tracking (for both recovery and forensic purposes).
Why they’re an up-and-comer? InterGuard is a cloud-based solution designed to bolster security in a world increasingly moving to the cloud and to mobile devices, such as smartphones and tablets. The company is backed by $6 million in VC and private funding and is both revenue and cash-flow positive.
One of key features of the InterGuard suite is that when a device is lost or stolen, InterGuard will track what’s happening on the device. In industries rife with corporate espionage and IP theft, if a thief logs into an email account, you’ll have a record of it. If the person signs into Facebook or some other social networking site, you’ll know who they are. And, of course, with built-in geolocation, you’ll be able to alert the authorities to track them down and recover the device.
Customers include NASA, the Department of Justice, Allstate, IBM and Wells Fargo.
What Problem Do they Solve? Within virtualized environments, maintaining security without hindering end user accessibility can seem like an uphill battle. Too often, one is sacrificed for the other – and security is what is most often sacrificed. Gartner studies report that up to 60% of virtualization environments are less secure than their physical counterparts, leading the enterprise to be understandably apprehensive when it comes to virtualization and cloud computing.
Moreover, a majority of breaches are caused by simple misconfigurations or inappropriate user privileges. In a virtual environment, a single misconfiguration, if exploited, could lead to a major incident.
What they Do: Instead of focusing only on the security requirements of VM operating systems, HyTrust addresses security, multi-tenancy and compliance for both cloud and virtual environments. The HyTrust virtual appliance provides access control, policy enforcement, and audit-quality logging for vSphere, Nexus and UCS.
Why they’re an up-and-comer? HyTrust addresses a key vulnerability in an increasingly large market. Without policy enforcement and access control, virtual and cloud environments pose serious risks. The company is backed by $16 million in funding from Cisco Systems, Granite Ventures, Trident Capital and Epic Ventures. Customers include Pepsi, AMD, GEICO, State of Michigan, US Navy, Netflix, and Hudson News.
What Problem Do they Solve? Malware. Viruses. Web-based worms. No matter how small the network a bevy of new and increasingly dangerous security threats loom just beyond the perimeter. Attackers are increasingly quick to discover new vulnerabilities and to exploit them.
Thus, taking a proactive approach to managing patches and plugging known vulnerabilities must be a priority for IT.
To adapt to new threats, many organizations have turned to deep-packet-level inspection. But small- to medium-sized businesses have different needs – and smaller budgets – than larger enterprises. SMBs have limited funds and few (or no) personnel to devote to endpoint management. Many also lack the necessary security expertise to repel evolving threats, even if they do have the bodies to throw at the problem. These businesses need a lower-cost, turnkey solution for their patch, asset and security remediation needs.
What they Do: Shavlik’s Cloud Patch is a web-based scanner that detects missing security patches for both the OS and third-party products that are installed locally. Using Shavlik’s technologies, any IT administrator can launch the Shavlik scanner through a browser. The scanner will then agentlessly detect all of the missing security patches. Scanning is executed without forcing IT to change firewall ports or otherwise lower the security perimeter. Cloud Patch also delivers tools for asset management and remediation.
Why they’re an up-and-comer? While a majority of competitors are taking a perimeter management approach to securing SMB networks, Shavlik is one of the few security vendors offering a scanning and patch-management solution from the cloud. This approach delivers a more flexible, scalable solution with significantly lower TCO.
Shavlik has been around for almost 20 years, so why are they an up-and-comer? Simple: cloud security is a land grab right now, and Shavlik is busy grabbing land in the much neglected SMB space. Shavlik claims 200,000 customers worldwide, and says it has delivered over 600,000 patches to tens of thousands of endpoints worldwide.
Several security partners have embedded Shavlik’s technology into their own solutions, including BMC, Dell KACE, Symantec and Scriptlogic.
What Problem Do they Solve: Commerce and online sales will only continue to rise in the coming years. Forrester Research projectsthat by 2014, US online sales will comprise nearly 8% of all retail sales in the country, equaling almost $250 billion dollars. For thieves, though, the steady growth of online sales presents countless opportunities.
Unlike brick and mortar retailers, online merchants only have credit card numbers and a few key personal identifiers to rely on when processing online transactions. Inherent limitations to the market (e.g., you can’t check the person’s ID over the web) make it tough to sort out the frauds from valued consumers. And with more retailers moving to a multichannel sales model to increase online presence and revenue, there is also the potential threat of vulnerabilities in making this transition online.
What they Do: Verifi’s solution to this problem starts with analyzing a company’s transaction history and comparing it to historical data. This data is used to develop specific rules for the merchant that prevent fraud but don’t over-reject transactions. Merchants then tailor and scale a solution to their specific needs and experience. Verifi’s software works with partner solutions, like ThreatMetrix (included in last week’s article. Verifi works with partner solutions to leverage multiple data points before accepting a transaction. A few examples include geo-location, device finger-printing, internal databases and fraud filters.
Why they’re an up-and-comer? Online fraud is an enormous problem, and anything to help e-merchants cope will have a decent chance of success. The US Department of Commerce stated that in Q3 2010 ecommerce sales increased 14.1% compare to the year prior, versus 5.8% over the same period for physical retail. Ecommerce currently represents only about 5% of the total sales in the US, so there’s huge room for growth. Verifi intends to capitalize on that growth by mitigating the risks that will plague those moving their sales online.
What Problem Do they Solve? Clients want to ensure that their confidential information – such as financial and personal information – is safe from theft. But critical information must be available on demand for various business processes. If traditional encryption methods are not compliant with data in the cloud, this inhibits the data from being accessed at critical moments.
What they Do: Voltage enables the protection of confidential enterprise data when it’s in use in, being processed in, or stored in the cloud in a way that allows it to still be used for a variety of business processes. This is accomplished by cryptographic technologies and simplified key management. Identity-Based Encryption (IBE), Format-Preserving Encryption (FPE) and tokenization, data masking and other technologies allow data to be protected inside and outside the cloud. Even if external attackers or malicious insiders gain access to the data, they won’t be able to decipher it.
Why they’re an up-and-comer? According to Ponemon Institute, enterprises now spend, on average, more than $6.65 million to recover from a single data breach. Entire security spaces, such as DLP, have emerged to target the breach-prevention market.
Voltage is backed by more than $42 million in VC funding and has an impressive client and partner roster, including Heartland Payment Systems, Microsoft, AT&T, CUNA Mutual, Kodak, Wells Fargo, WatchGuard, and Websense.
What Problem Do they Solve? It’s no secret that the perimeter, hardware-based networking and security model doesn’t quite work in the cloud. Traditional edge networking and security has not been modernized the way server and storage infrastructure has been over the past decade. According to Vyatta, the next generation of infrastructure must be delivered as an application that maps to the elastic model of the cloud in order to keep up.
Some vendors in hardware-based routing and security are tying services to virtual switches or providing firewall-only virtual machines, both of which represent a continuation of the sort of vendor lock that many organizations are hoping the cloud will break. This doesn’t just fall short of meeting cloud network architecture requirements (on-demand, elastic, mobile, platform neutral, limited footprint), but it also limits cloud developers’ ability to properly protect virtual machines and users in a multi-tenant environment.
What they Do: The platform-independent Vyatta Network OS virtual machine is a bridging, routing and network security (firewall, IPS, IPSec & SSL VPN, web filtering+, layer 2 cloud bridging) solution for cloud computing platforms. Vyatta addresses the complex automation, migration and advanced security needs of hosted public cloud data and centralized private clouds by enabling cloud architects to design complete n-tier networks within a hypervisor environment. Vyatta’s solution is delivered on-demand and can be used on a per-customer or per-server basis.
Why they’re an up-and-comer? The company is backed by more than $28 million in VC funding and claims to have over one thousand customers and tens of thousands of software and appliance installations around the world. Fortune 500 customers include Toyota, EMC, Honeywell and CBS.
What Problem Do they Solve? Data breaches, insider threats and cloud-based vulnerabilities all tax traditional security. For instance, when employees at an organization fall victim to an attack, be it a phishing attack or malware on a device used for both business and personal use, they can unknowingly bring malware into the corporate network, which can easily add up to millions of dollars in productivity or IP loss.
Additionally, addressing the issues of regulating a mobile workforce and providing advanced content scanning are both issues that put such a large burden on IT that many organizations can’t keep up.
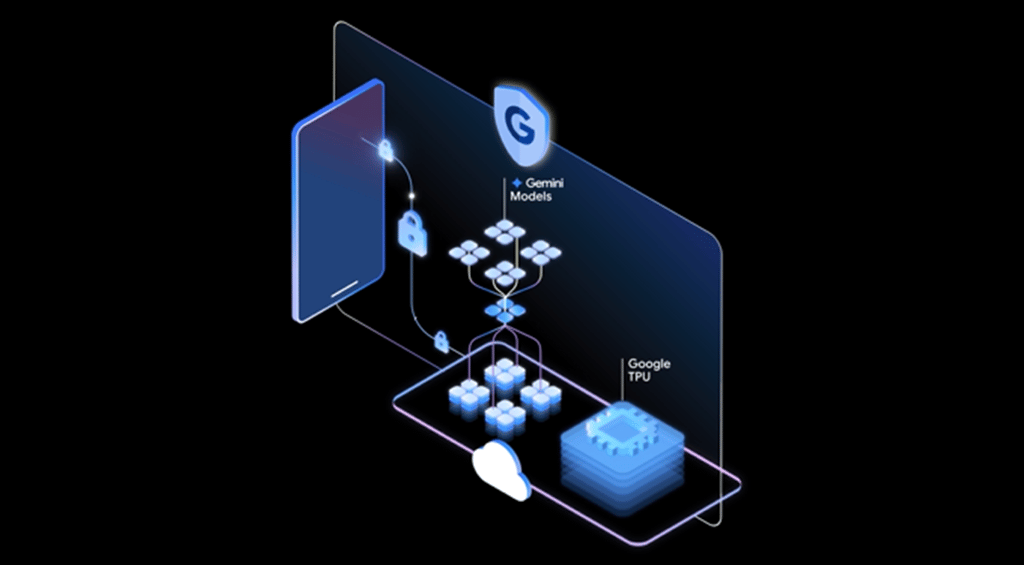
What they Do: Zscaler provides “policy-based secure internet access for any employee, on any device, anywhere.” Through “innovations in its massively scalable cloud architecture,” the Zscaler Security Cloud provides an ultra-low latency SaaS security solution that requires neither hardware nor software to function properly.
Zscaler’s cloud security service suite offers anti-virus, anti-spyware, anti-spam, URL filtering, Web 2.0 control, bandwidth control, mail flow control, and Data Loss Prevention (DLP). Large enterprises and small businesses can take advantage of the cloud to secure their employees at much lower TCO than traditional solutions.
Why they’re an up-and-comer? In just two years, Zscaler’s cloud security service has grown to over 40 data centers, processing over a billion transactions a day to secure millions of enterprise, SMB and Service Provider customers. According to the company, this growth is due to major advancements in service architecture, scanning speed and capacity, and logging and reporting. Zscaler claims that it can actually scan every byte of data to provide the most comprehensive security across web and email traffic.
Customers include La-Z-Boy, HDFC (India’s largest home mortgage company), HCR ManorCare, LANCO Group and Crutchfield.
-
Ethics and Artificial Intelligence: Driving Greater Equality
FEATURE | By James Maguire,
December 16, 2020
-
AI vs. Machine Learning vs. Deep Learning
FEATURE | By Cynthia Harvey,
December 11, 2020
-
Huawei’s AI Update: Things Are Moving Faster Than We Think
FEATURE | By Rob Enderle,
December 04, 2020
-
Keeping Machine Learning Algorithms Honest in the ‘Ethics-First’ Era
ARTIFICIAL INTELLIGENCE | By Guest Author,
November 18, 2020
-
Key Trends in Chatbots and RPA
FEATURE | By Guest Author,
November 10, 2020
-
Top 10 AIOps Companies
FEATURE | By Samuel Greengard,
November 05, 2020
-
What is Text Analysis?
ARTIFICIAL INTELLIGENCE | By Guest Author,
November 02, 2020
-
How Intel’s Work With Autonomous Cars Could Redefine General Purpose AI
ARTIFICIAL INTELLIGENCE | By Rob Enderle,
October 29, 2020
-
Dell Technologies World: Weaving Together Human And Machine Interaction For AI And Robotics
ARTIFICIAL INTELLIGENCE | By Rob Enderle,
October 23, 2020
-
The Super Moderator, or How IBM Project Debater Could Save Social Media
FEATURE | By Rob Enderle,
October 16, 2020
-
Top 10 Chatbot Platforms
FEATURE | By Cynthia Harvey,
October 07, 2020
-
Finding a Career Path in AI
ARTIFICIAL INTELLIGENCE | By Guest Author,
October 05, 2020
-
CIOs Discuss the Promise of AI and Data Science
FEATURE | By Guest Author,
September 25, 2020
-
Microsoft Is Building An AI Product That Could Predict The Future
FEATURE | By Rob Enderle,
September 25, 2020
-
Top 10 Machine Learning Companies 2021
FEATURE | By Cynthia Harvey,
September 22, 2020
-
NVIDIA and ARM: Massively Changing The AI Landscape
ARTIFICIAL INTELLIGENCE | By Rob Enderle,
September 18, 2020
-
Continuous Intelligence: Expert Discussion [Video and Podcast]
ARTIFICIAL INTELLIGENCE | By James Maguire,
September 14, 2020
-
Artificial Intelligence: Governance and Ethics [Video]
ARTIFICIAL INTELLIGENCE | By James Maguire,
September 13, 2020
-
IBM Watson At The US Open: Showcasing The Power Of A Mature Enterprise-Class AI
FEATURE | By Rob Enderle,
September 11, 2020
-
Artificial Intelligence: Perception vs. Reality
FEATURE | By James Maguire,
September 09, 2020
SEE ALL
CLOUD ARTICLES